OPTIMIZED PAIRWISE MASTER KEY IDENTIFIER BASED ROAMING FOR WI-FI PROTECTED ACCESS 3 SIMULTANEOUS AUTHENTICATION OF EQUALS WITH WIRELESS LOCAL AREA NETWORK CONTROLLER OR ACCESS POINT | Semantic Scholar
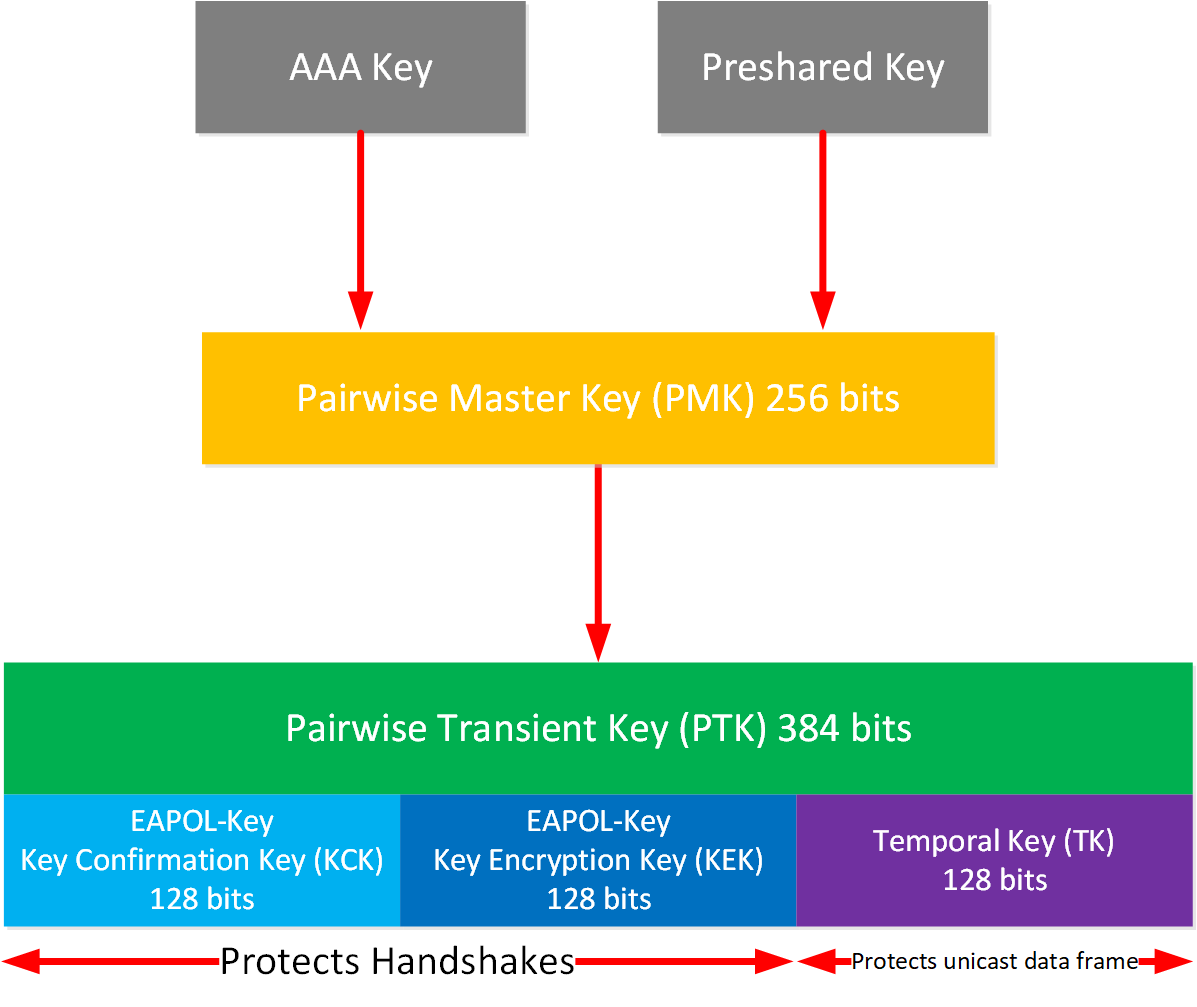
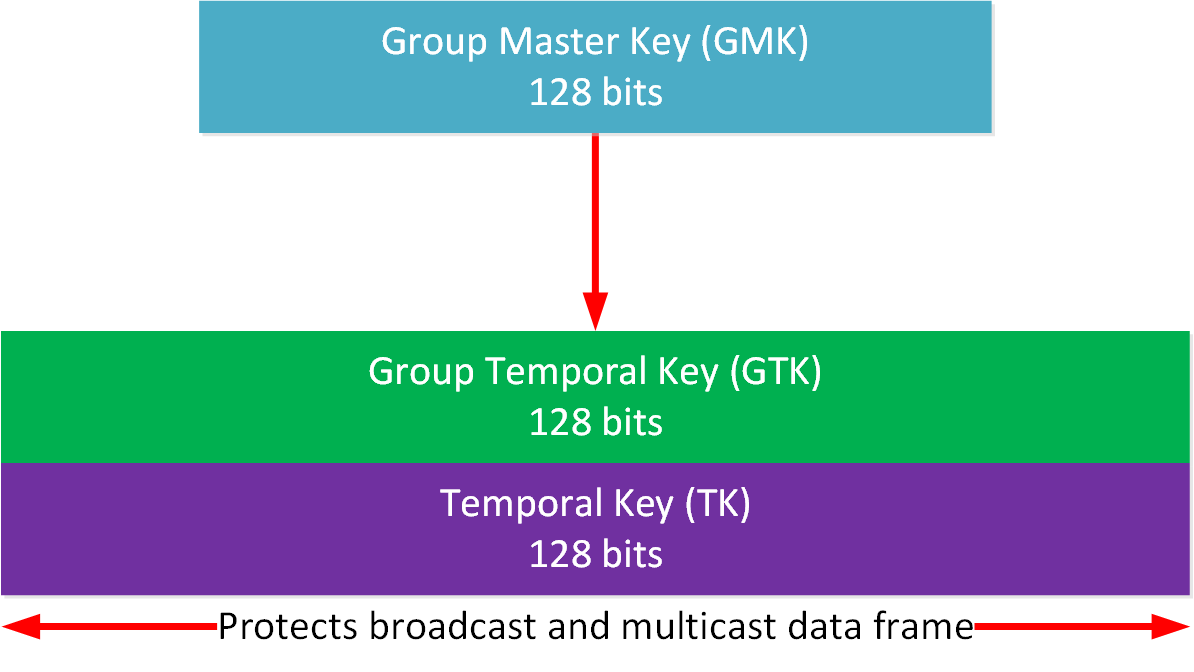
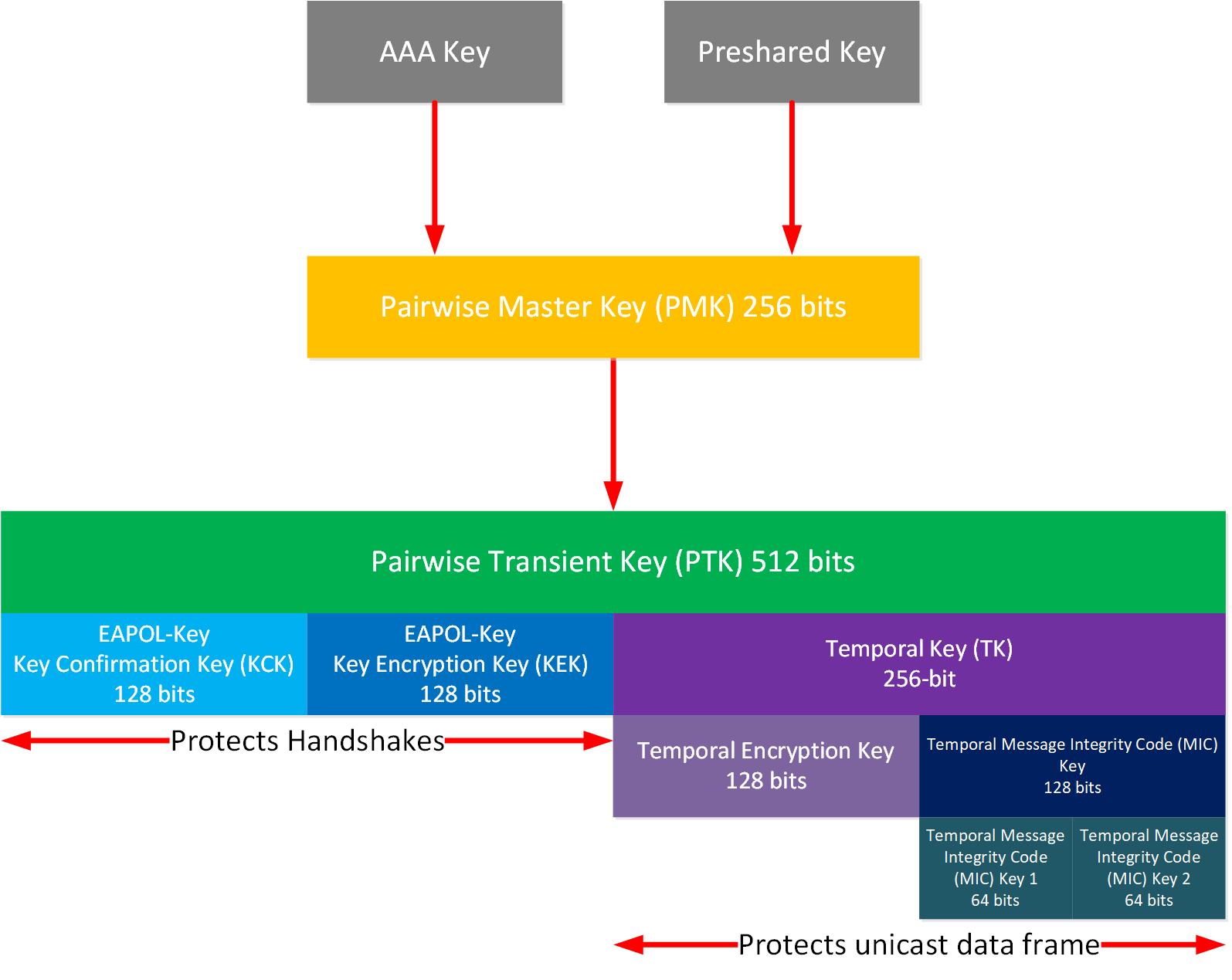
Key Management :: Chapter 8. WLAN Encryption and Data Integrity Protocols :: Wireless lan security :: Networking :: eTutorials.org
OPTIMIZED PAIRWISE MASTER KEY IDENTIFIER BASED ROAMING FOR WI-FI PROTECTED ACCESS 3 SIMULTANEOUS AUTHENTICATION OF EQUALS WITH W

OPTIMIZED PAIRWISE MASTER KEY IDENTIFIER BASED ROAMING FOR WI-FI PROTECTED ACCESS 3 SIMULTANEOUS AUTHENTICATION OF EQUALS WITH WIRELESS LOCAL AREA NETWORK CONTROLLER OR ACCESS POINT | Semantic Scholar

New attack on WPA/WPA2 using Pairwise Master Key Identifier (PMKID). | New attack on WPA/WPA2 using Pairwise Master Key Identifier (PMKID). https://hashcat.net/forum/thread-7717.html In this video, I will describe a new... | By

OPTIMIZED PAIRWISE MASTER KEY IDENTIFIER BASED ROAMING FOR WI-FI PROTECTED ACCESS 3 SIMULTANEOUS AUTHENTICATION OF EQUALS WITH WIRELESS LOCAL AREA NETWORK CONTROLLER OR ACCESS POINT | Semantic Scholar

SEE2PK: Secure and energy efficient protocol based on pairwise key for hierarchical wireless sensor network | Peer-to-Peer Networking and Applications

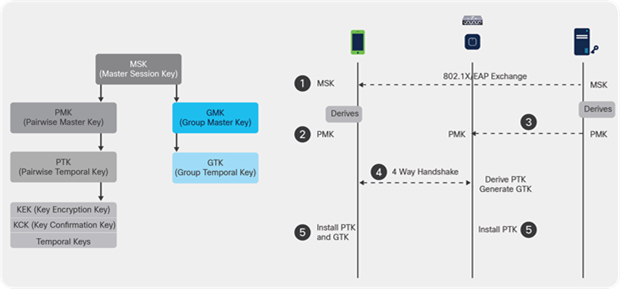
![802.11 Network Security Fundamentals [Cisco Secure Services Client] - Cisco Systems 802.11 Network Security Fundamentals [Cisco Secure Services Client] - Cisco Systems](https://www.cisco.com/en/US/i/200001-300000/200001-210000/203001-204000/203835.jpg)